MusiKey Authentication Developed Originally by Graham Hartridge
contact: [email protected]
Check out MusiKey on: github
Updated on Feb 27 , 2026
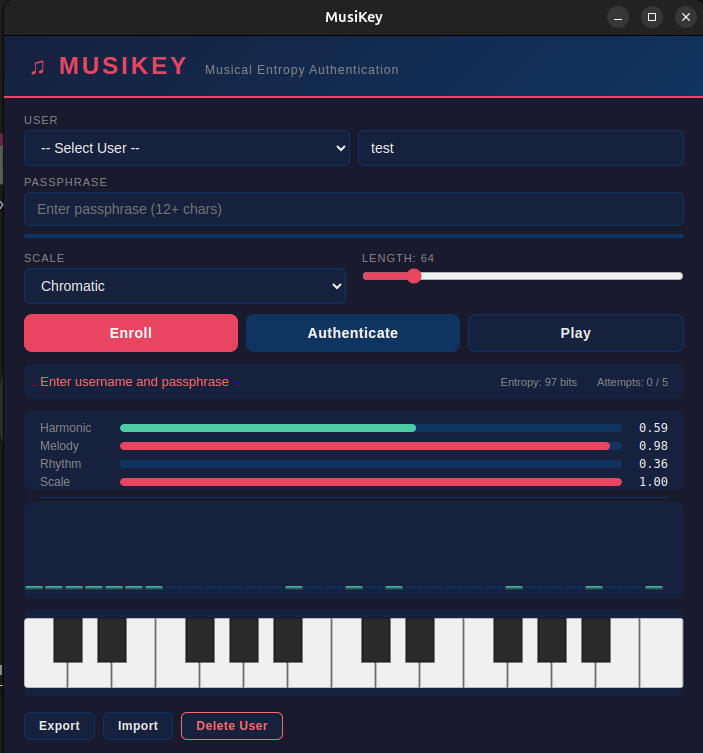
MusiKey — Musical Entropy AuthenticationYour password is a song. MusiKey replaces passwords with algorithmically generated musical compositions that double as cryptographic keys — audible, recognizable, and carrying 112+ bits of entropy.The Problem
Passwords are weak, reused, and forgettable. Hardware tokens are expensive and losable. Biometrics can't be changed if compromised. Authentication shouldn't require choosing between security and usability.How It Works
Enroll — Choose a passphrase and musical scale. MusiKey generates a unique composition and encrypts it under cascaded military-grade cryptography.Authenticate — Enter your passphrase. The system decrypts your song, verifies its musical integrity across four dimensions, and plays it back through an animated piano and frequency visualizer.Protect — Wrong passphrase? Exponential rate limiting kicks in. Five failed attempts permanently destroy the credential. No brute forcing possible.Features
ECDSA P-256 challenge-response authentication for external services (MusiKey Protocol) — a more secure alternative to 6-digit TOTP codes
Multi-factor authentication: musical challenge-response + time-based one-time passwords
Visual fingerprint — a unique visual hash of your credential you can recognize at a glance
Cascaded KDF: PBKDF2 (600,000 iterations) + Argon2id (128MB memory-hard)
Double AES-256-GCM encryption with machine-bound keys
Tamper-detected audit logging with cryptographic chain integrity
Credential self-destruct after 5 failed attempts
Seven musical scales, configurable composition length (32–256 notes)
Real-time piano keyboard and frequency bar visualizer
Encrypted-at-rest storage with HMAC verification and key splitting
Passphrase strength enforcement with entropy calculation
Automatic memory zeroing of sensitive data
Credential export, import, and encrypted cross-device sync
Zero runtime dependencies — all crypto via native platform APIs
Dark-themed interface
Security
20+ layered security mechanisms including: cascaded key derivation (PBKDF2 + Argon2id), double AES-256-GCM encryption, ECDSA P-256 asymmetric authentication, zero-knowledge proof commitments, encrypted-at-rest credential storage, machine-bound key derivation with deep hardware fingerprinting, HMAC tamper detection, key splitting across isolated stores, monotonic signature counters for clone detection, exponential backoff rate limiting, passphrase strength enforcement, credential integrity hashing, automatic memory zeroing, and permanent self-destruct.Built With
Electron · TypeScript · Web Crypto API · Web Audio API · Node.js Argon2id